Security
The GnuPG Project takes the security of software it develops very seriously. In general we prefer a full disclosure approach and all bugs listed in our bug tracker as well as code changes in our software repository are public. Given that GnuPG is an important part of many software distributions and severe bugs in GnuPG would affect their users directly, we co-ordinate with them in private as soon as we learn about a severe vulnerability.
Sometimes we receive pre-notifications of research which may lead to a new kind of vulnerability. In these cases we may work with the researchers in private on a solution and co-ordinate our fix release with them.
Threat Model of libgcrypt
Libgcrypt has been developed for use in a wide variety of platforms with different security needs. Some platforms exhibit fine-grained side channels which can be used to spy on processes running in other containers or virtual machines. Although Libgcrypt implements many countermeasures against such side-channels attacks, it is not possible to avoid all of them. In the worst case it is thus possible to leak the entire private key or a password to a malicious process running in another virtual machine on the same hardware.
Those hardware related threats are out of scope in Libgcrypt's threat model. It is up to users not to offer any access to those side-channels.
Security contact
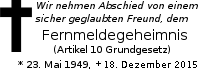
If you found a severe security problem and you do not want to publish it, please report it by mail to security at gnupg.org. We prefer reports in plain text format; if needed we can also work with PDF files. For security reasons we won't read any other complex data formats (e.g. docx or odt).
Note that we do not use a team OpenPGP key. Thus please write a non-encrypted message to the security address and ask for the keys of the developers at duty and then encrypt the mail to all of them. A list of our core developers can be found here; they are all active on the gnupg-devel mailing list.